Executive Summary
- Who this is for: Solution Architects, Technical Architects, Engineering Leads
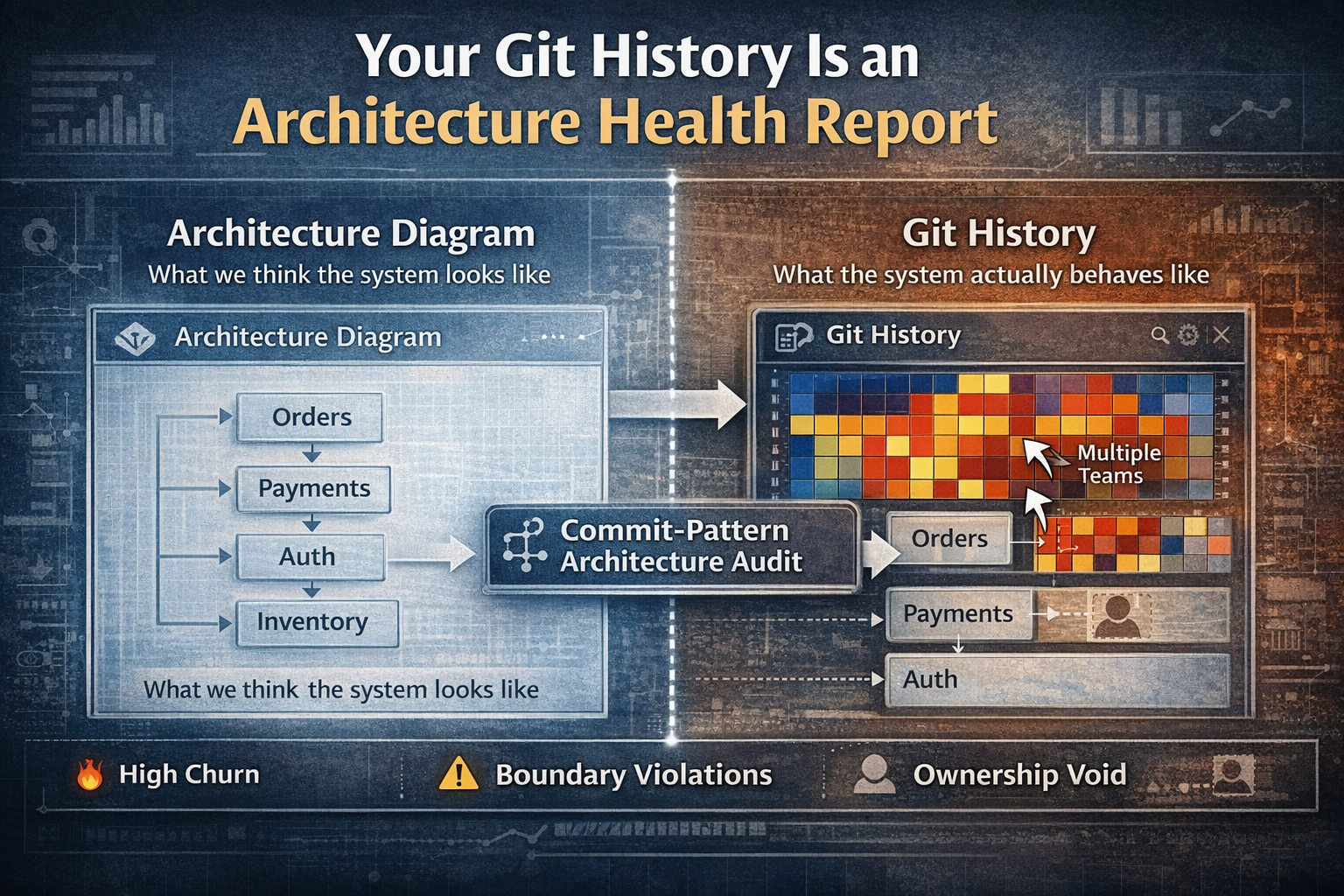
- Problem it solves: Architecture reviews rely on diagrams and governance documents that often fail to reflect the real system structure
- Key outcome: A practical method to detect architectural instability, boundary violations, and ownership gaps using Git commit patterns
- Time to implement: 2–4 weeks to introduce structural analysis
- Business impact: Early detection of architectural drift, clearer system ownership, and improved architecture governance
The Hidden Architecture Signal in Your Repository
Most architecture reviews examine artifacts like:
- Architecture diagrams
- Governance documents
- System design presentations
- Architecture review board decisions
These artifacts describe how the system is supposed to look.
But software systems evolve through code changes, not diagrams.
Every day engineers commit changes that reveal:
- where complexity accumulates
- which modules are unstable
- which teams are crossing boundaries
- which parts of the system have been abandoned
This signal already exists.
Inside your Git history.
Yet most organizations never analyze it.
The Building Inspector Analogy
Imagine a building inspector evaluating structural health.
They could review architectural blueprints.
But that would only show design intent.
A better signal would be something else.
They would inspect:
- which walls have been patched repeatedly
- which beams have been reinforced multiple times
- which areas receive constant repair work
Repeated repairs indicate structural stress.
In software systems, commit churn plays the same role.
Frequent changes to the same components often indicate architectural instability.
The Architecture Reality Gap
Architecture leaders often review:
- design documentation
- architecture diagrams
- governance approvals
Meanwhile, engineering teams interact with a completely different reality.
The repository shows:
- which modules change constantly
- which components are touched by many teams
- which domains receive little or no maintenance
These signals often contradict official architecture documentation.
Both realities exist at the same time.
But very few organizations connect them.
The Commit-Pattern Architecture Audit (CPAA)
To reveal the real structure of a system, introduce a simple technique:
Commit-Pattern Architecture Audit (CPAA).
CPAA analyzes Git commit history and maps patterns to architecture domains.
This reveals structural health indicators invisible in architecture diagrams.
Three signals are particularly valuable.
The Three Signals Hidden in Git History
Churn measures how frequently files or modules change.
High churn often indicates:
- unstable design
- unclear boundaries
- frequent refactoring
- evolving requirements
Example indicators:
- modules modified in nearly every release
- components constantly patched after deployments
- repeated bug fixes in the same area
High churn does not always mean bad engineering.
But persistent churn often signals structural stress in the architecture.
2. Boundary Violations: Too Many Teams Touching the Same Component
Healthy architecture maintains clear ownership boundaries.
Git history can reveal when those boundaries break.
If many teams frequently modify the same files or modules, it may indicate:
- unclear module ownership
- tightly coupled components
- architectural boundaries that exist only in diagrams
Example signal:
A payments module being modified by teams responsible for:
- checkout
- billing
- subscriptions
- reporting
This suggests the boundary is not functioning as intended.
3. Ownership Voids: Abandoned Domains
Another important signal is lack of commits.
Some parts of the system receive little attention over long periods.
This may indicate:
- abandoned modules
- undocumented legacy components
- fragile systems teams avoid modifying
These components often become risk hotspots.
When changes are eventually required, they become expensive and dangerous.
The Architecture Heatmap
Once commit data is analyzed, the insights become powerful when visualized.
A common approach is to create a Git churn heatmap mapped to architecture domains.
Example visualization layers:
Layer 1 — Code Churn
- frequency of commits per module
Layer 2 — Team Touchpoints
- which teams modify which components
Layer 3 — Architectural Domains
- mapping code to system modules or bounded contexts
Combined together, this reveals:
- structural instability zones
- boundary violations
- ownership voids
This transforms Git history into a live architecture health report.
Why This Matters for Architects
Architecture diagrams describe intended structure.
Git history reveals operational reality.
When these two diverge, architectural drift begins.
Commit-pattern analysis helps architects:
- detect structural instability early
- identify modules needing redesign
- clarify ownership boundaries
- detect neglected system areas
Instead of relying only on design reviews, architects gain empirical signals from real engineering activity.
Implementation Guide (30 Days)
Introducing Commit-Pattern Architecture Audits does not require complex tooling.
A simple approach can begin quickly.
Phase 1: Extract Commit Metrics (Weeks 1–2)
Analyze repository history for:
- commit frequency by file or module
- number of contributors per component
- churn trends across releases
Tools that help include:
- Git analytics tools
- repository mining scripts
- engineering analytics platforms
Success Metric:
Clear visibility into high-churn areas.
Phase 2: Map Commits to Architecture Domains (Weeks 2–3)
Link repository paths to architectural modules.
Example mapping:
/orders/* → Orders Domain
/payments/* → Payments Domain
/inventory/* → Inventory Domain
Success Metric:
Commit activity can be interpreted in architectural context.
Phase 3: Introduce Structural Reviews (Week 4)
In architecture reviews, analyze:
- highest churn components
- modules modified by many teams
- inactive system areas
Use these insights to guide:
- refactoring priorities
- module boundary clarification
- ownership reassignment
Success Metric:
Architecture discussions incorporate repository evidence.
Evidence from Practice
Organizations that analyze commit patterns often discover:
- modules with extreme change frequency
- architectural boundaries violated in practice
- legacy components nobody owns
- hotspots responsible for recurring incidents
These insights frequently contradict official architecture diagrams.
But they reveal something more important.
The real architecture of the system.
Action Plan
This Week
Ask three questions:
- Which components in your system change the most?
- Which files are modified by the largest number of teams?
- Which parts of the system have not been touched for a year?
If these answers are unclear, your architecture visibility may be incomplete.
Next 30 Days
Introduce a simple Git-based architecture audit.
Start tracking:
- code churn by module
- cross-team modification patterns
- inactive system areas
3–6 Months
Integrate commit-pattern analysis into:
- architecture reviews
- technical debt discussions
- system redesign decisions
Architecture governance becomes stronger when it reflects how systems actually evolve.
Final Thought
Architecture diagrams show design intent.
Architectural Decision Records capture reasoning.
But Git history reveals structural reality.
Every commit is a signal.
Every change reveals where the system is under pressure.
Your architecture health report already exists.
It has been sitting quietly in your repository the whole time.
Turn Your Repository Into an Architecture Insight Engine
If architecture reviews rely only on diagrams…
if system instability appears without warning…
or if architectural drift is difficult to detect —
your organization may be missing a critical signal.
In a focused 30-minute Architecture Health Diagnostic, we will:
- Analyze whether your repositories reveal structural instability
- Identify architectural hotspots based on commit patterns
- Detect ownership gaps across system domains
- Introduce a lightweight Commit-Pattern Architecture Audit model
No architecture theater.
No excessive governance layers.
No abstract design debates.
Just architecture insights derived from how your system actually evolves.
→ Book an Architecture Strategy Session
or
Your architecture leaves traces in every commit.
The question is whether you are reading them.